heading
-
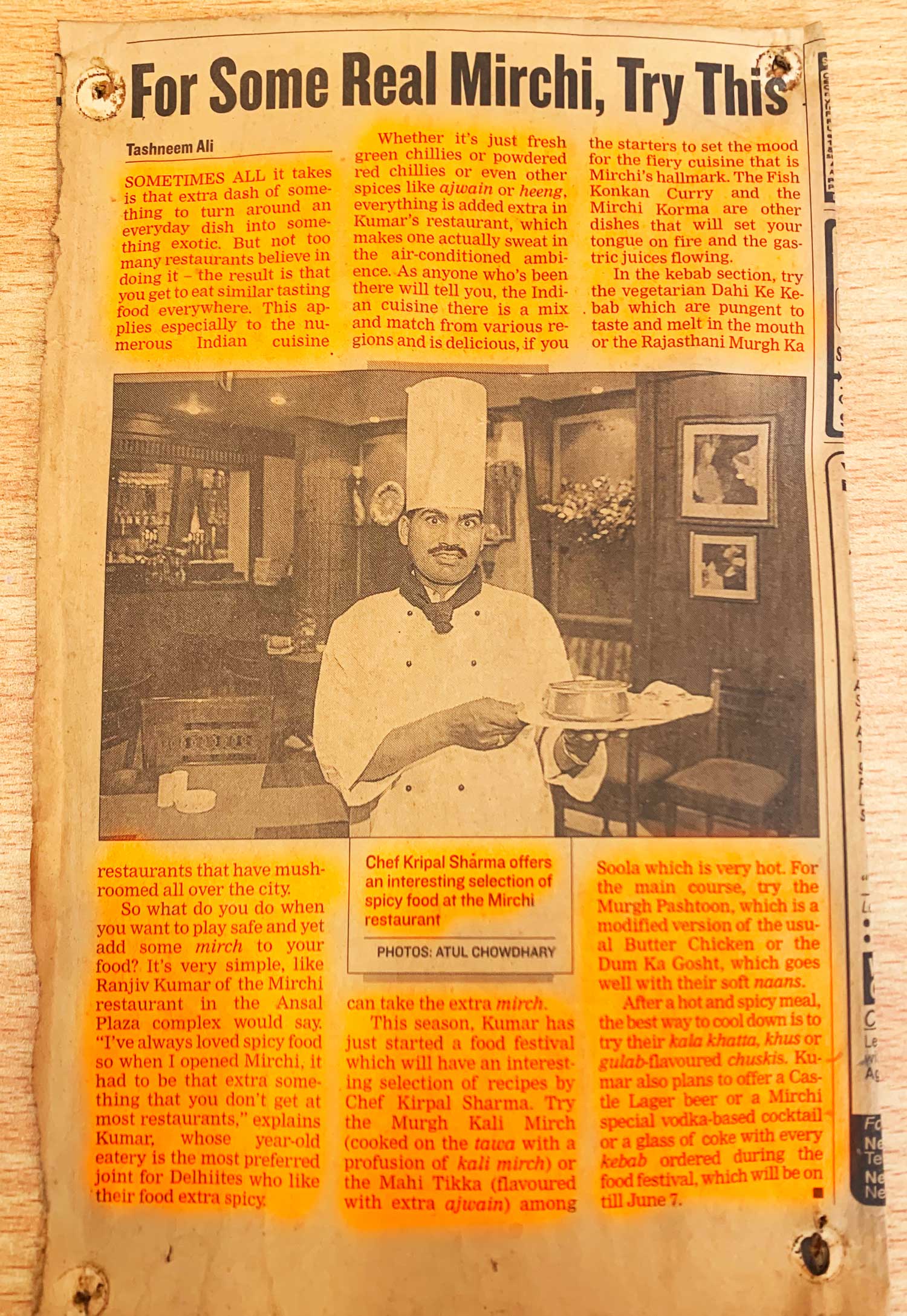
Delicious food at your door step.The name MIRCHI denotes a bold and un-conservative kind of authentic Indian cuisine.
It is not just another bland, ultra-conservative, traditional Tandoori and Mughlai Food restaurant.